Recent searches
Search options
Oooooooof
> Malicious code was discovered in the upstream tarballs of xz, starting with version 5.6.0. The tarballs included extra .m4 files, which contained instructions for building with automake that did not exist in the repository.
Fear not, xz users, a new developer has stepped up to take over the project:
Tia Jan <jant1203@proton.me>
The backlash thread on GitHub is already well underway: https://github.com/tukaani-project/xz/issues/92
Guy has Go project that wraps xz to provide native Go bindings. Project has had no commits for THREE YEARS.
Suddenly some guy sends a PR to update the version of xz in use to the backdoored version:
https://github.com/jamespfennell/xz/pull/2
Then you got some guy in the HN comments astroturfing everyone claiming that he knows the guy who submitted the PR IRL and he's a "cool dude", or something.
All this shit is so sus.
CAN THE FUCKING FEDS PLEASE STOP BACKDOORING OPEN SOURCE SOFTWARE PLEASE? K THANKS
oh yeah, and the guy who submitted the PR supposedly works at 1Password.
So that's nice.
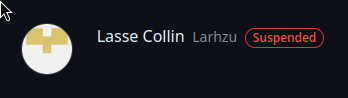
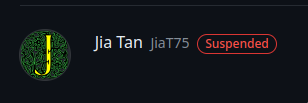
Both of the maintainer accounts for the xz (under the https://github.com/tukaani-project) have been suspended, presumably by Github staff:
The suspension isn't listed on the account profile, but visible in the Following/Followers list for some reason, ex: https://github.com/JiaT75?tab=following
@eriner explain what this means
@John The post you're commenting on is a bit in the weeds. At a high level, the xz compression library was intentionally subverted by one of the project maintainers and a backdoor was inserted. This impacted SSH on Debian and Fedora, two very popular linux distros.
The best high-level writeup I can find is Michael Larabel's: https://www.phoronix.com/news/XZ-CVE-2024-3094
@Derdnik @John This specific attack was at least one year in the making. In particular, this commit: https://github.com/tukaani-project/xz/commit/ee44863ae88e377a5df10db007ba9bfadde3d314
and then the disabling of ifunc in google/oss-fuzz to hide the vulnerability: https://github.com/google/oss-fuzz/pull/10667
This attack didn't happen overnight, but also suggests that, given the extensive planning and setup that precipitated this backdoor, there very well may be other intentionally introduced bugs; the simple reversion of xz to a prior version may not be sufficient.